Providing Additional Layer of Protection through Domain Names Filtering
DNS-based malware is threatening the business networks as it is often used to steal critical company and customer data, interrupt business continuity and damage brand reputation. However, traditional security systems are not enough to mitigate this type of threat as they can't distinguish between normal and malicious domains, and not to mention to block access to specific domains when filtering traffic by destinations.
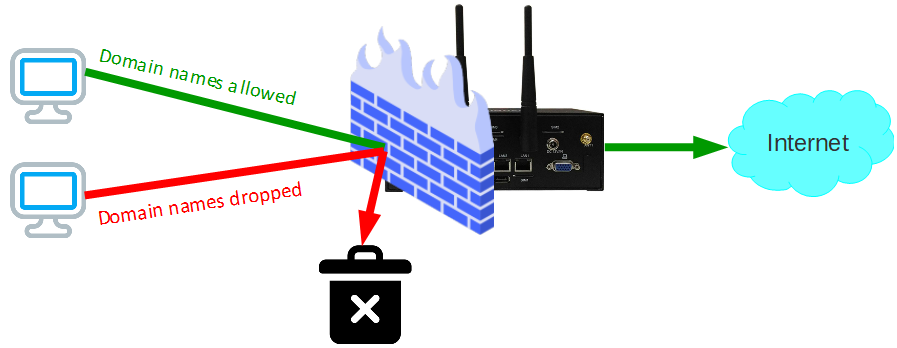
A DNS firewall is embedded in the Q-Balancer appliances and provides a purpose-built and complementary solution to traditional enterprise network security systems. It prevents network users and systems from connecting known-malicious sites. DNS firewall adds a layer of security by selectively intercepting DNS resolution for known-malicious network assets including domain names, IP addresses, and name servers.
> Domain Names Filtering
DNS Firewall
A DNS Firewall prevents network users and systems from connecting known-malicious sites. Q-Balancer's inbuilt DNS Firewall works by employing DNS Response Policy Zones (RPZs) and operable threat intelligence; it provides insights on threats, and helps isolate infected devices for remediation. The DNS Firewall can help block:
> Phishing-related domains
When the DNS Firewall is enabled, the office user who attempts to access the phishing site will be prevented from doing so, and is therefore protected from the potential threat that could cause.
> Malware-related domains
Q-Balancer inbuilt DNS Firewall protects enterprises against cyber attacks that use DNS to communicate with command-and-control (C&C) malwares.
> Botnet command and control
Q-Balancer inbuilt DNS Firewall helps IT rapidly pinpoint compromised devices, isolating them and preventing their DNS communications with malicious C&C servers and botnets. With the visibility to the blocked DNS queries, you can identify the infected hosts with the information such as domain name, IP address, time, etc., which is helpful for improved threat remediation and security response.
Top Benefits
> Fortified network security
> Enhanced compliance
> Mitigated network security threat
> Improved productivity
> Visibility to the domains blocked